Sharepoint
Provide the new connection with a Name here. You can give this connection a short description in the box below.Enter the User and Password in the Authentication area, this is the user you want to use to access SharePoint. The user entered here is solely needed to access the service metadata in the Portal Manager.
OAuth2/OpenID Connect (from Intrexx 8 with Online Update 05)
The method OAuth2 supports servers that require an OAuth2 authorization for users. Should the service support an auto approval of the user, the login of a user can be specified here for the metadata. If this isn't possible, the metadata document must first of all be saved as a local file and stored in the Intrexx OData configuration directory of the portal (File name: <SERVICE_GUID>.edmx).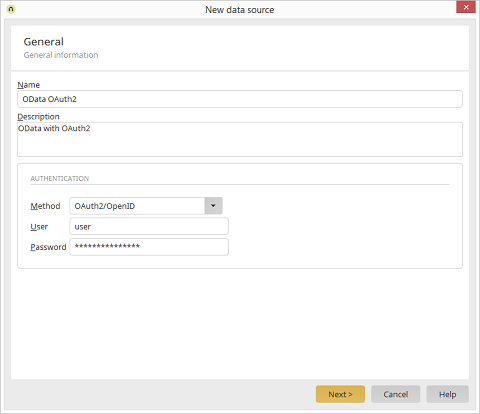
Currently, the actual configuration of the OAuth2 authorization must be performed in the XML configuration file of the OData consumer directly (File <INTREXX_HOME>/org/portal/internal/cfg/odata/<SERVICEGUID>.xml). The following properties are relevant here:
<property name="authenticationType" value="OAUTH2"/> // Value must be OAUTH2
<property name="oauth2.scope" value="<OAuth Scopes>"/>
<property name="oauth2.authenticationScheme" value="<Schema>"/>
<property name="oauth2.clientId" value="<Client ID>"/>
<property name="oauth2.grantType" value="<Grant Type>"/>
<property name="oauth2.clientAuthenticationScheme" value="<Client Schema>"/>
<property name="oauth2.userAuthorizationUri value="<Endpoint for the authentication>"/>
<property name="oauth2.clientSecret"value="<Client Secret>"/>
<property name="oauth2.redirectUri" value="<Redirect URL>"/>
<property name="oauth2.accessTokenUri" value="<Endpoint for the request of a token>"/>
Spring Security OAuth2 Identity Provider
<?xml version="1.0" encoding="UTF-8"?>
<odata xmlns="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg consumer.xsd">
<consumer description="" guid="30378A6DEDA601F69D525C7FCAFA7E12CEC114C8" name="SpringOAuth2">
<property name="authenticationType" value="OAUTH2"/>
<property name="additionalAuthenticationTypes" value=""/>
<property name="userName" value="user"/>
<property name="password" value="E54F94C0106981A41312FC14955B164C"/>
<property name="servicePrincipalName" value=""/>
<property name="isSharePointService" value="false"/>
<property name="isSapService" value="false"/>
<property name="sapUseDefaultClientId" value="false"/>
<property name="sapClientId" value=""/>
<property name="sapNetweaverGatewayHost" value=""/>
<property name="sapNetweaverGatewayPort" value=""/>
<property name="sapNetweaverGatewayUseSSL" value="false"/>
<property name="sapSolutionManagerRegistered" value="false"/>
<property name="authTypeSource" value=""/>
<property name="authLoginSource" value=""/>
<property name="authPasswordSource" value=""/>
<property name="authSapClientIdSource" value=""/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="form"/>
<property name="oauth2.accessTokenUri" value="http://localhost:9999/uaa/oauth/token"/>
<property name="oauth2.userAuthorizationUri" value="http://localhost:9999/uaa/oauth/authorize"/>
<property name="oauth2.scope" value="openid"/>
<property name="oauth2.clientId" value="acme"/>
<property name="oauth2.clientSecret" value="acmesecret"/>
<property name="oauth2.redirectUri" value="http://localhost/devportal/oauth2"/>
<services>
<service guid="E2050082619BBD33EEDEA97BDCC9223B25244191" name="SpringOauth2" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="http://localhost:8888/res/" useSSL="false"/>
</services>
<userMappings/>
</consumer>
</odata>
Microsoft SharePoint 365 (OAuth2 via AzureAD)
<?xml version="1.0" encoding="UTF-8"?>
<odata xmlns="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg consumer.xsd">
<consumer description="" guid="A07EFC374A42F1A4C2C0BEDB60E5B99B2F89F660" name="SharePoint365">
<property name="authenticationType" value="OAUTH2"/>
<property name="oauth2.scope" value="Site.Read Web.Read List.Write"/>
<property name="oauth2.clientId" value="CLIENT_ID"/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="form"/>
<property name="oauth2.authenticationScheme" value="form"/>
<property name="oauth2.userAuthorizationUri" value="https://company.sharepoint.com/_layouts/15/OAuthAuthorize.aspx"/>
<property name="oauth2.clientSecret" value="CLIENT_SECRET"/>
<property name="oauth2.redirectUri" value="https://localhost/devportal/oauth2"/>
<property name="oauth2.accessTokenUri" value="https://accounts.accesscontrol.windows.net/TENANT_ID/tokens/OAuth/2"/>
<property name="sharePoint.oauth2.resource" value=".../company.sharepoint.com@TENANT_ID"/>
<property name="sharePoint.oauth2.realm" value="TENANT_ID"/>
<services>
<service guid="0EA408C8493C29D52921D6E78389A2A5CD1E2539" name="SharePoint365" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="https://company.sharepoint.com/_vti_bin/listdata.svc/" useEtag="true" useSSL="true"/>
</services>
<userMappings/>
</consumer>
</odata>
OData
Authentication Types
In the Authentication area, select the Method required by the service: None for anonymous access, Basic for basic HTTP, Intrexx for Intrexx OData Services, Kerberos for services with integrated Windows authentication, Kerberos (HTTP Basic) for services with Windows or standard authentication, or X.509 for X.509 client certificates.Basic Authentication
If you select the Basic method, the login information will be requested. The user entered here will only be needed to access the service metadata in the Portal Manager.Intrexx Authentication
The Intrexx method is useful for services provided with the Intrexx OData Provider. Login information will be transferred encrypted in this way. For access to metadata, enter an Intrexx user and corresponding password here as well.Integrated Windows Authentication
The options for Kerberos and Kerberos (HTTP Basic) are available for Windows environments to use Windows Integrated Authentication for Single Sign-On. The second option for HTTP Basic enables authentication for clients that do not support the Kerberos protocol.Please note the following basic requirements for successful authentication with Kerberos:
- The Intrexx portal must be run with integrated authentication. You can enable this in the Users module via the Configuration menu.
- The users from your Active Directory must be correspondingly created in Intrexx. You can quickly and easily import these users in the Users module by selecting the menu item Users / Users and groups Import. Please make sure that at least one user is included in the Administrators group, so that the system may continue to be managed.
- The server on which Intrexx is installed requires the group policy Delegation.
- All clients and servers must be members of the same domain.
- In Internet Explorer, the security settings for the used zone must have the user authentication setting of Automatic logon with current user name and password. Additionally, the option for Enable integrated Windows authentication must be selected in the advanced settings.
If a user cannot be authenticated, the second option will automatically use the standard login method.
For successful authentication, it is necessary to specify a Service Principal Name (SPN). The SPN contains information about the service that requires a Kerberos ticket to be generated for it. This ticket is required for the Internet Information Server used by the Intrexx portal server.
The SPN is generally constructed as follows:
http/< computer-DNS-name>@<KERBEROS_REALM>
Computer-DNS-name: Fully qualified host name (such as mycomputer.mycompany.com)
KERBEROS_REALM: Generally the domain in uppercase letters (such as MYCOMPANY.COM).
The SPN would therefore look like the following using the sample data:
http/mycomputer.mycompany.com@MYCOMPANY.COM
Authentication with X.509 Certificates
When you select the X.509 method, a certificate store in PKCS12 format can be uploaded. Later, each user can upload their own certificate store using a login form.For authentication with X.509 certification, the root certificate of the authentication authority, which is responsible for issuing the client certificates, must previously have been imported into Intrexx. The root certificate can be saved using the Portal / Portal properties / Certificates menu. Restart the portal server afterwards.
OAuth2/OpenID Connect (from Intrexx 8 with Online-Update 05)
The method OAuth2 supports servers that require an OAuth2 authorization for users. Should the service support an auto approval of the user, the login of a user can be specified here for the metadata. If this isn't possible, the metadata document must first of all be saved as a local file and stored in the Intrexx OData configuration directory of the portal (File name: <SERVICE_GUID>.edmx).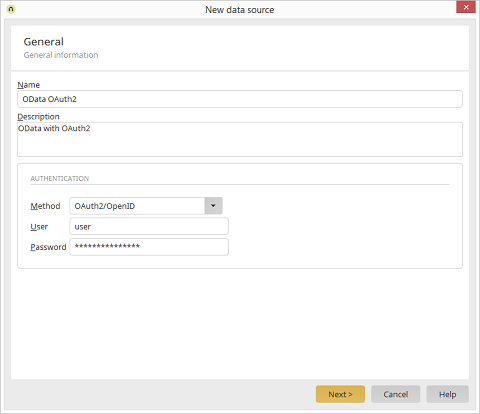
Currently, the actual configuration of the OAuth2 authorization must be performed in the XML configuration file of the OData consumer directly (File <INTREXX_HOME>/org/portal/internal/cfg/odata/<SERVICEGUID>.xml). The following properties are relevant here:
<property name="authenticationType" value="OAUTH2"/> // Value must be OAUTH2
<property name="oauth2.scope" value="<OAuth Scopes>"/>
<property name="oauth2.authenticationScheme" value="<Schema>"/>
<property name="oauth2.clientId" value="<Client ID>"/>
<property name="oauth2.grantType" value="<Grant Type>"/>
<property name="oauth2.clientAuthenticationScheme" value="<Client Schema>"/>
<property name="oauth2.userAuthorizationUri value="<Endpoint for the authentication>"/>
<property name="oauth2.clientSecret"value="<Client Secret>"/>
<property name="oauth2.redirectUri" value="<Redirect URL>"/>
<property name="oauth2.accessTokenUri" value="<Endpoint for the request of a token>"/>
Spring Security OAuth2 Identity Provider
<?xml version="1.0" encoding="UTF-8"?>
<odata xmlns="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg consumer.xsd">
<consumer description="" guid="30378A6DEDA601F69D525C7FCAFA7E12CEC114C8" name="SpringOAuth2">
<property name="authenticationType" value="OAUTH2"/>
<property name="additionalAuthenticationTypes" value=""/>
<property name="userName" value="user"/>
<property name="password" value="E54F94C0106981A41312FC14955B164C"/>
<property name="servicePrincipalName" value=""/>
<property name="isSharePointService" value="false"/>
<property name="isSapService" value="false"/>
<property name="sapUseDefaultClientId" value="false"/>
<property name="sapClientId" value=""/>
<property name="sapNetweaverGatewayHost" value=""/>
<property name="sapNetweaverGatewayPort" value=""/>
<property name="sapNetweaverGatewayUseSSL" value="false"/>
<property name="sapSolutionManagerRegistered" value="false"/>
<property name="authTypeSource" value=""/>
<property name="authLoginSource" value=""/>
<property name="authPasswordSource" value=""/>
<property name="authSapClientIdSource" value=""/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="form"/>
<property name="oauth2.accessTokenUri" value="http://localhost:9999/uaa/oauth/token"/>
<property name="oauth2.userAuthorizationUri" value="http://localhost:9999/uaa/oauth/authorize"/>
<property name="oauth2.scope" value="openid"/>
<property name="oauth2.clientId" value="acme"/>
<property name="oauth2.clientSecret" value="acmesecret"/>
<property name="oauth2.redirectUri" value="http://localhost/devportal/oauth2"/>
<services>
<service guid="E2050082619BBD33EEDEA97BDCC9223B25244191" name="SpringOauth2" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="http://localhost:8888/res/" useSSL="false"/>
</services>
<userMappings/>
</consumer>
</odata>
Microsoft SharePoint 365 (OAuth2 via AzureAD)
<?xml version="1.0" encoding="UTF-8"?>
<odata xmlns="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="urn:schemas-unitedplanet-de:lucy:server:odata:consumer:cfg consumer.xsd">
<consumer description="" guid="A07EFC374A42F1A4C2C0BEDB60E5B99B2F89F660" name="SharePoint365">
<property name="authenticationType" value="OAUTH2"/>
<property name="oauth2.scope" value="Site.Read Web.Read List.Write"/>
<property name="oauth2.clientId" value="CLIENT_ID"/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="form"/>
<property name="oauth2.authenticationScheme" value="form"/>
<property name="oauth2.userAuthorizationUri" value="https://company.sharepoint.com/_layouts/15/OAuthAuthorize.aspx"/>
<property name="oauth2.clientSecret" value="CLIENT_SECRET"/>
<property name="oauth2.redirectUri" value="https://localhost/devportal/oauth2"/>
<property name="oauth2.accessTokenUri" value="https://accounts.accesscontrol.windows.net/TENANT_ID/tokens/OAuth/2"/>
<property name="sharePoint.oauth2.resource" value=".../company.sharepoint.com@TENANT_ID"/>
<property name="sharePoint.oauth2.realm" value="TENANT_ID"/>
<services>
<service guid="0EA408C8493C29D52921D6E78389A2A5CD1E2539" name="SharePoint365" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="https://company.sharepoint.com/_vti_bin/listdata.svc/" useEtag="true" useSSL="true"/>
</services>
<userMappings/>
</consumer>
</odata>
Microsoft Outlook Online (only http, no OData)
<property name="authenticationType" value="OAUTH2"/> // Value must be OAUTH2
<property name="oauth2.scope" value="https://outlook.office.com/mail.read"/>
<property name="oauth2.authenticationScheme" value="form"/>
<property name="oauth2.clientId" value="<Client ID>"/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="form"/>
<property name="oauth2.userAuthorizationUri value="https://login.microsoftonline.com/common/oauth2/v2.0/authorize"/>
<property name="oauth2.clientSecret"value="<Client Secret>"/>
<property name="oauth2.redirectUri" value="http://localhost/devportal/oauth2"/>
<property name="oauth2.accessTokenUri" value= "https://login.microsoftonline.com/common/oauth2/v2.0/token"/>
<services>
<service guid="XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX" name="Outlook" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="https://outlook.office.com/api/v2.0/me/messages" useSSL="true"/>
</services>
GoogleMail (only http, no OData)
<property name="authenticationType" value="OAUTH2"/> // Value must be OAUTH2
<property name="oauth2.scope" value="https://mail.google.com/"/>
<property name="oauth2.authenticationScheme" value="header"/>
<property name="oauth2.clientId" value="<Client ID>"/>
<property name="oauth2.grantType" value="authorization_code"/>
<property name="oauth2.clientAuthenticationScheme" value="header"/>
<property name="oauth2.userAuthorizationUri value="https://accounts.google.com/o/oauth2/auth"/>
<property name="oauth2.clientSecret"value="<Client Secret>"/>
<property name="oauth2.redirectUri" value="http://localhost/devportal/oauth2"/>
<property name="oauth2.accessTokenUri" value= "https://accounts.google.com/o/oauth2/token"/>
<services>
<service guid="XXXXXXXXXXXXXXXXXXXXXXXXXXXXX" name="GMail Inbox" odataSpecVersion="V2" sapCsrfTokenRequired="false" serviceRootURI="https://www.googleapis.com/gmail/v1/users/firstname.lastname@googlemail.com/messages/" useSSL="true"/>
</services>